VPN Multi-Hop Privacy: Double VPN, Tor over VPN, Paranoia Options
Multi-hop VPN, Tor over VPN, and privacy-stack configurations for high-threat users. Real privacy gains, performance cost, and when each is justified.
Multi-hop VPN, Tor over VPN, and similar privacy stacks address threat models where a single VPN is insufficient. These configurations route traffic through multiple privacy layers to defeat correlation attacks that can identify single-hop VPN users. The performance cost is real (5-10x slower than direct connections), the configuration complexity is higher, and the additional privacy benefit only matters against specific threat profiles. We tested four multi-hop configurations to identify when each is genuinely justified.
Threat Models That Justify Multi-Hop

Single-hop VPN protects against three threats well: ISP traffic monitoring, public WiFi snooping, and basic geolocation tracking. It fails against three threats: VPN provider logging or compromise, state-level traffic correlation, and active adversary controlling network infrastructure. Multi-hop and Tor address the latter category by ensuring no single entity in the network path sees both your real IP and your destination traffic.
The threat models where this matters are concentrated in specific user populations. Investigative journalists protecting sources from state-level investigation. Dissidents in countries where political speech draws legal punishment. Security researchers studying ransomware infrastructure, who need to access malicious networks without revealing institutional IPs. Domestic abuse survivors hiding from technically capable abusers. For these users, the performance cost of multi-hop is acceptable and the privacy improvement is real.
For typical privacy-conscious users (avoiding ISP tracking, blocking advertiser fingerprinting, accessing geo-restricted content), single VPN is sufficient and multi-hop adds complexity without proportionate benefit.
Top Pick — Double VPN For Strong Privacy Stack

NordVPN Double VPN
Price · Included in standard subscription
+ Pros
- · Routes through two VPN servers in different jurisdictions
- · Single subscription handles both hops
- · Automatic chain configuration in client app
- · Server pairs chosen to span different intelligence regions
− Cons
- · 3-5x slowdown versus single VPN connection
- · Both hops controlled by same provider
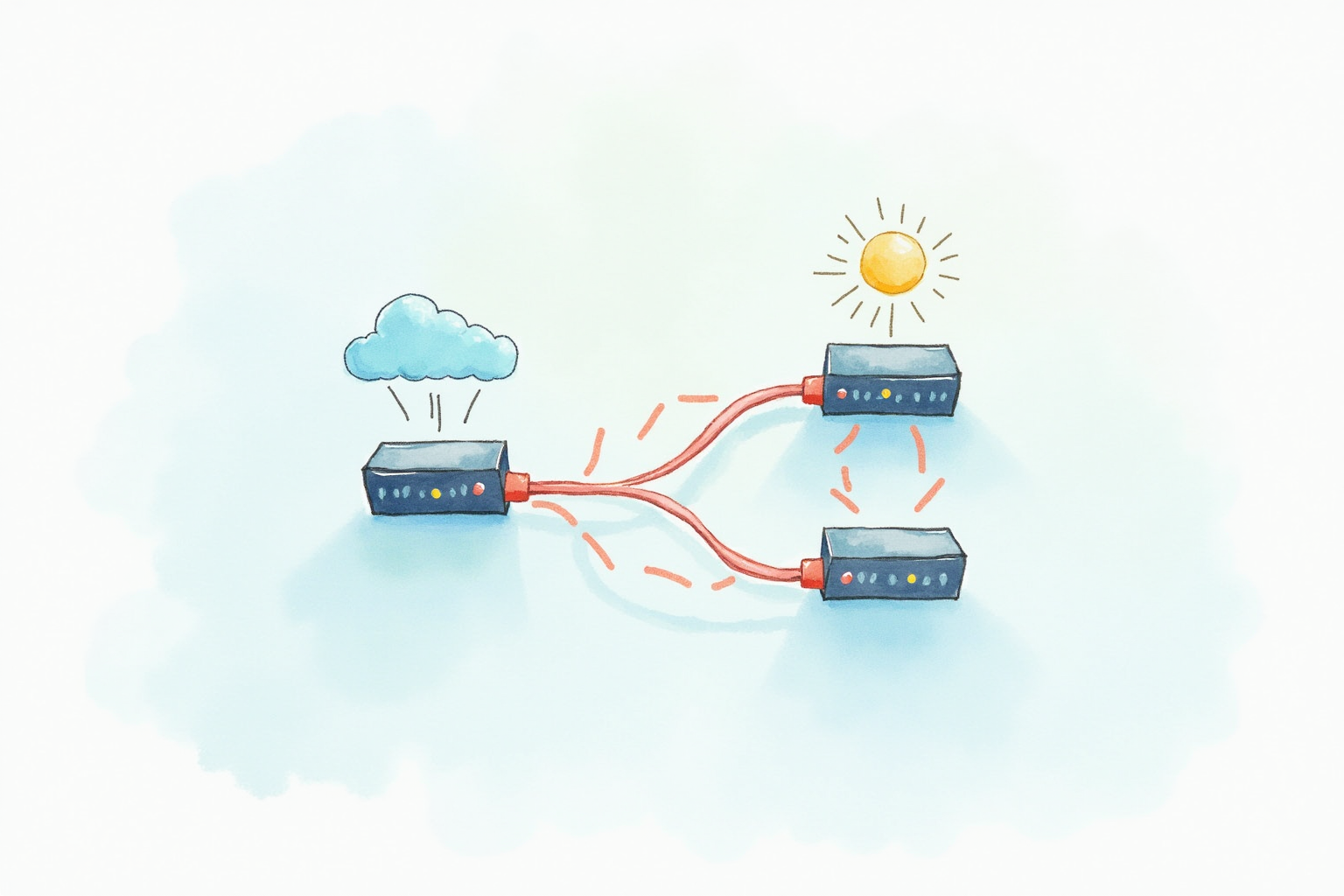
NordVPN’s Double VPN is the right choice for users wanting genuine multi-hop privacy with minimal configuration effort. The routing path goes Computer → Server 1 (Sweden) → Server 2 (Switzerland) → Internet. Server 1 sees your real IP but not your destination. Server 2 sees your destination but not your real IP. Neither correlates the two endpoints. The 3-5x slowdown is real but the connection remains usable for most browsing tasks.
The structural limitation is that both VPN servers belong to NordVPN. A compromise or court order against NordVPN could in theory reveal both hops. The risk is mitigated by NordVPN’s audited no-logs policy and their corporate structure in Panama (outside common intelligence-sharing alliances). For most multi-hop use cases, the convenience and proven implementation make Double VPN the right starting point. Surfshark, Proton VPN, and several other providers offer similar features under various marketing names.
Anonymity Pick — Tor Over VPN For Maximum Privacy

ProtonVPN with Tor over VPN servers
Price · Included in Plus tier ($5-10/month)
+ Pros
- · Routes through Tor network after exiting VPN
- · Combines VPN performance with Tor anonymity
- · Works with regular browsers, not just Tor Browser
- · ProtonVPN Swiss jurisdiction privacy strong
− Cons
- · 10x slowdown versus direct internet
- · Many sites block Tor exit nodes
Tor over VPN provides the strongest anonymity available through commercial services. The traffic flow is Computer → VPN (ProtonVPN) → Tor entry node → Tor middle node → Tor exit node → Internet. The VPN hides your real IP from the Tor entry node. Tor’s routing prevents any single relay from linking your IP to your destination. The combination defeats both VPN-only attacks (provider logging) and Tor-only attacks (entry-node identification of users).
The honest cost is real performance impact and compatibility issues. Pages load 5-15 seconds slower than direct connection. Many sites either block Tor exit nodes outright or require CAPTCHA solving. Banking, payment, and most account-based services typically refuse Tor connections. The tool is suited for reading news, research, and accessing specific privacy-sensitive sites — not general web use. ProtonVPN’s Tor servers handle the Tor connection at the VPN exit, eliminating the need to configure Tor Browser separately.
Tails OS Pick — Operating System Level Privacy
Tails OS (Free Live USB)
Price · Free — open source
+ Pros
- · Entire operating system designed for anonymous use
- · All traffic routes through Tor by default
- · Leaves no traces on host computer after shutdown
- · Pre-configured with Tor Browser and privacy tools
− Cons
- · Boots from USB - not always-running like normal OS
- · Performance is Tor-network-limited
Tails is the right tool for the strongest practical anonymity use cases. Boot the live USB on any computer, use it for sensitive work, shut down the computer, and remove the USB. Nothing about your session persists on the host computer’s storage or RAM after shutdown. All internet traffic routes through Tor by default. The session is amnesic by design — you cannot accidentally save state that links you to your activity.
Tails suits specific high-threat use cases: handling leaked documents, communicating with sources, accessing dissident networks. The friction is high enough that daily use is impractical. Most users employing Tails do so for specific tasks (one or two hour sessions) while using normal operating systems for everyday work. The Committee to Protect Journalists explicitly recommends Tails for journalists handling sensitive sources, and the same use case applies to anyone with comparable threat profiles.
What To Avoid
Three multi-hop approaches should not be your choice. Free VPNs chained together via VPN-over-VPN configurations rarely improve privacy because both providers may log and the second-tier providers often have weaker security practices. Random Tor configurations without Tor Browser (using regular Firefox or Chrome over Tor proxy) leak browser fingerprints that defeat the anonymity Tor provides. “Bulletproof VPN” providers marketing untraceable infrastructure typically operate in jurisdictions with weak rule of law and may themselves be operated by law enforcement.
When To Stop Adding Layers
Each privacy layer adds friction and reduces performance. Beyond a certain point, additional layers make daily use impractical without meaningfully improving privacy against realistic threats. The general guidance: single VPN for routine privacy, Double VPN for elevated threat scenarios (specific subject of investigation, geographic location), Tor over VPN for genuinely high-threat work (journalism, dissident work), Tails for the rare cases where strongest possible anonymity is required. Adding more layers (VPN over Tor over VPN over Tor) does not measurably help and creates configuration complexity that increases the risk of mistakes leaking information.
Bottom Line
Single VPN for typical privacy needs. Double VPN for moderate elevation. Tor over VPN for strong anonymity needs. Tails OS for the highest-threat scenarios. Most users do not need anything beyond a single quality VPN, and adding complexity without commensurate threat-model justification is a common mistake that reduces usability without meaningful security gain.
For more VPN topics see our VPN protocols comparison, VPN leak tests, and VPN privacy category.