Enterprise MFA Solutions 2026: Okta vs Duo vs Microsoft Entra ID
We deployed three enterprise MFA platforms to a 50-user test org. Adaptive authentication, SSO integration, cost, and the picks by company size.
Enterprise MFA platforms consolidate authentication across all your business applications into one centrally-managed system. They replace the chaos of per-app 2FA settings with consistent policy, audit logging, and adaptive risk-based authentication. We deployed Okta, Duo Security (Cisco), and Microsoft Entra ID (formerly Azure AD) to a 50-user test organization over eight weeks. We measured initial setup complexity, end-user adoption resistance, integration with common business applications, and total cost of ownership including hidden migration costs.
What Enterprise MFA Adds Over Per-App 2FA
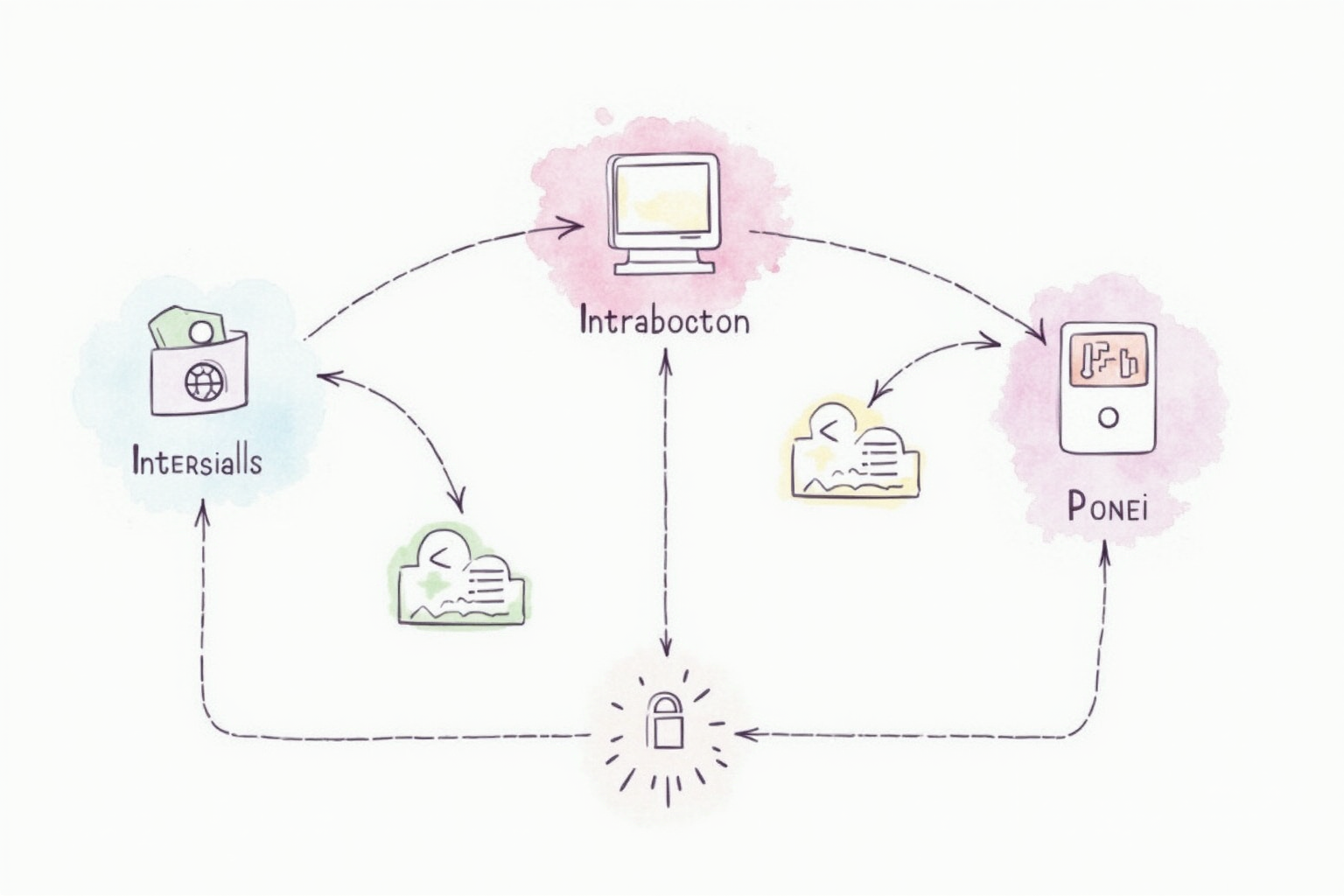
Three structural capabilities justify the enterprise MFA cost over relying on individual application 2FA settings. First, centralized policy enforcement — administrators define authentication requirements once, applied consistently across all integrated applications. When a new employee joins, MFA enrolls automatically as part of identity provisioning. When an employee leaves, MFA deprovisioning revokes access immediately across all applications. Without centralized MFA, each application requires manual configuration and offboarding.
Second, adaptive authentication based on context signals. A user signing in from their assigned laptop, known location, during work hours might bypass MFA after initial authentication. The same user signing in from a new device, foreign country, at 3am triggers additional authentication factors and may notify security teams. This context awareness reduces friction for legitimate access while strengthening protection against compromise scenarios.
Third, audit logs spanning all integrated applications. Every authentication attempt across hundreds of applications appears in one searchable log, with risk scoring and analytics that surface patterns invisible to per-app logs. For compliance frameworks (SOC 2, HIPAA, PCI-DSS), the consolidated audit trail eliminates substantial manual effort during audits.
Top Pick — Best All-Round Enterprise MFA

Okta Workforce Identity
Price · $2-15/user/month based on features
+ Pros
- · Largest integration catalog with 7,000+ pre-built application connections
- · Strong adaptive authentication with built-in threat intelligence
- · Best documentation and partner ecosystem for complex deployments
- · Lifecycle management automation reduces manual provisioning
− Cons
- · Per-user pricing adds up at scale — total cost can exceed $20K annually for 100 users
- · Configuration complexity steep for organizations without dedicated security staff
Okta Workforce Identity is the right choice for organizations with diverse application portfolios and dedicated security or IT operations staff. The 7,000+ pre-built application integrations cover virtually every business SaaS in common use, eliminating the integration engineering required with alternatives. The adaptive authentication engine uses Okta’s threat intelligence feed (sourced from authentication patterns across thousands of customers) to identify novel attack patterns faster than per-customer detection allows.
The lifecycle management automation is the structural feature that pays for the per-user cost. New employee onboarding flows through Okta, automatically provisioning accounts in HR, email, file sharing, project management, and dozens of other applications. Departing employees deprovision similarly. The time savings for IT teams scales with company size and application diversity. The honest cost limitation is real — at 15 dollars per user monthly for full feature access, a 100-person organization spends 18,000 dollars annually on Okta alone, before the consulting hours required for initial deployment.
Microsoft Stack Pick — When Already On Microsoft 365
Microsoft Entra ID P1/P2
Price · $6/user/month (P1) or $9/user/month (P2)
+ Pros
- · Native integration with Microsoft 365 ecosystem
- · Conditional Access policies are the most powerful adaptive engine
- · Lower cost than Okta for Microsoft-centric organizations
- · Defender for Identity for hybrid AD environments
− Cons
- · Integration outside Microsoft ecosystem requires more work than Okta
- · Licensing complexity — features split across multiple SKUs
Microsoft Entra ID is the right choice for organizations already standardized on Microsoft 365 for email, productivity, and collaboration. The native integration with Outlook, Teams, SharePoint, OneDrive, and other Microsoft apps eliminates the integration friction that other identity platforms face. Conditional Access policies are the most powerful adaptive authentication engine we have used — granular rules can require different authentication based on user, device compliance status, application sensitivity, location, network, and dozens of other signals.
The Microsoft-centric design becomes a limitation for organizations with significant non-Microsoft applications. Integrating Slack, Atlassian products, Salesforce, AWS, or other major SaaS requires more configuration work and ongoing maintenance than Okta’s native connections. For mixed environments, the choice between Entra and Okta comes down to which ecosystem dominates — at 60+ percent Microsoft applications, Entra makes sense; below that, Okta’s broader integration catalog usually wins.
Simple Pick — Best Deployment Experience For Small Teams

Duo Security (Cisco) Essentials
Price · $3/user/month (Essentials) or $9/user/month (Premier)
+ Pros
- · Easiest deployment of major MFA platforms — typical setup in days
- · Native VPN, remote desktop, and SSH integration
- · Strong device trust verification before authentication
- · Cisco backing provides enterprise support and stability
− Cons
- · Fewer SaaS application integrations than Okta
- · Adaptive authentication less sophisticated than Entra Conditional Access
Duo Security is the right choice for smaller organizations or specific use cases (VPN access, remote desktop authentication, SSH session protection) where simplicity matters more than feature breadth. The Duo Push mobile app for authentication is widely considered the cleanest user experience among MFA platforms, which drives end-user adoption. Deployment to typical small organizations completes in days rather than weeks.
The native VPN integration is a particular strength. Pulse Secure, Cisco AnyConnect, Palo Alto GlobalProtect, and most enterprise VPN platforms support Duo as a primary MFA provider with minimal configuration. For organizations whose primary MFA need is securing remote access rather than comprehensive SSO, Duo delivers the core capability at lower cost and complexity than Okta or Entra. The honest limitation is SaaS integration breadth — Duo covers fewer applications than Okta and the integrations require slightly more manual configuration.
What To Avoid
Three enterprise MFA categories should not be your default. Free-tier authenticator apps (Google Authenticator, Microsoft Authenticator standalone) work for personal accounts but lack the centralized policy management that justifies enterprise MFA. Build-your-own MFA implementations on top of open-source identity tools (Keycloak, FreeIPA) work technically but require dedicated engineering resources most small businesses lack. Legacy on-premises MFA appliances (older RSA SecurID, hardware token systems) continue working but lack the adaptive authentication and SaaS integration that modern cloud platforms provide.
Deployment Strategy
Plan a phased rollout regardless of which platform you choose. Phase 1 (weeks 1-3): IT and security team deployment, testing all major integrations with these users, refining policies. Phase 2 (weeks 4-6): Pilot group of 10-20 users from each department, gathering feedback and refining. Phase 3 (weeks 7-12): Full rollout with mandatory enrollment by deadline, phased policy enforcement. Phase 4 (week 12+): Adaptive authentication policy refinement, conditional access tuning, audit logging implementation.
Skipping phases is the most common deployment failure pattern. Rushing to mandatory enforcement before the platform is properly configured generates user frustration that takes months to recover from. Patience pays back in adoption rates and long-term security posture.
Bottom Line
Okta for organizations with diverse SaaS applications and dedicated security operations. Microsoft Entra for Microsoft 365-heavy organizations wanting native integration. Duo for smaller organizations or VPN-focused use cases prioritizing deployment simplicity. The right choice depends on existing technology stack and organizational complexity more than feature differences.
For more enterprise security see our business password managers comparison, hardware security keys tested, and enterprise security category.